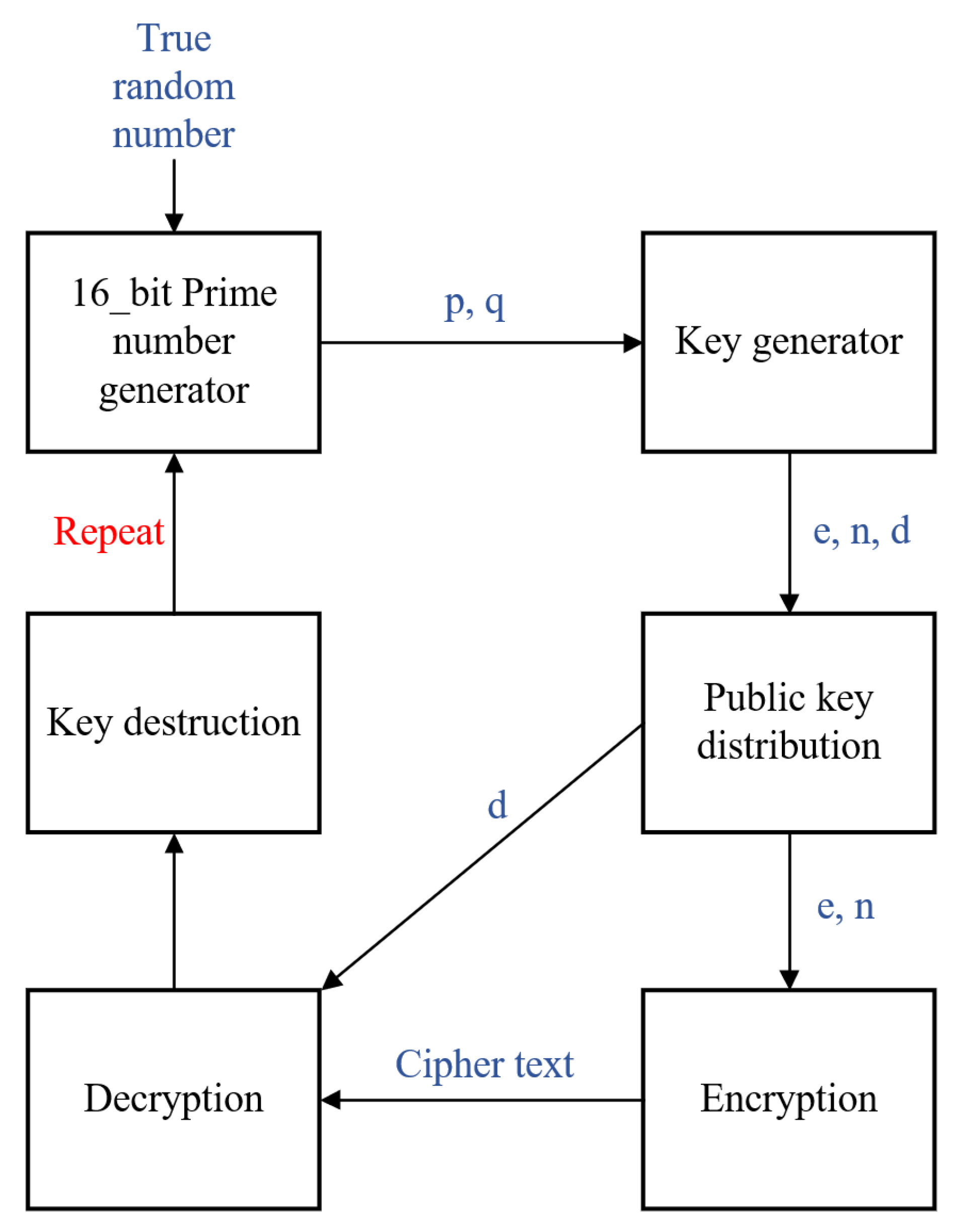
Electronics | Free Full-Text | New RSA Encryption Mechanism Using One-Time Encryption Keys and Unpredictable Bio-Signal for Wireless Communication Devices

Applied Sciences | Free Full-Text | Block Data Record-Based Dynamic Encryption Key Generation Method for Security between Devices in Low Power Wireless Communication Environment of IoT

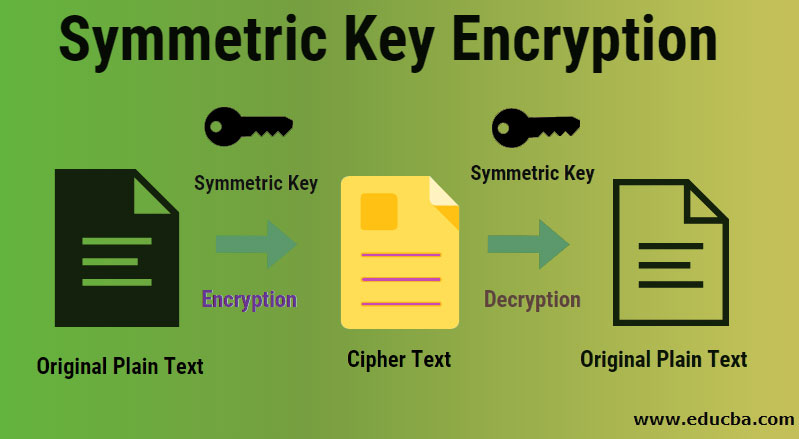
Symmetric Key Cryptography using Dynamic Key and Linear Congruential Generator (LCG) | Semantic Scholar

Securing color image transmission using compression-encryption model with dynamic key generator and efficient symmetric key distribution | Semantic Scholar